Let's learn about Network via these 46 free stories. They are ordered by most time reading created on HackerNoon. Visit the /Learn Repo to find the most read stories about any technology.
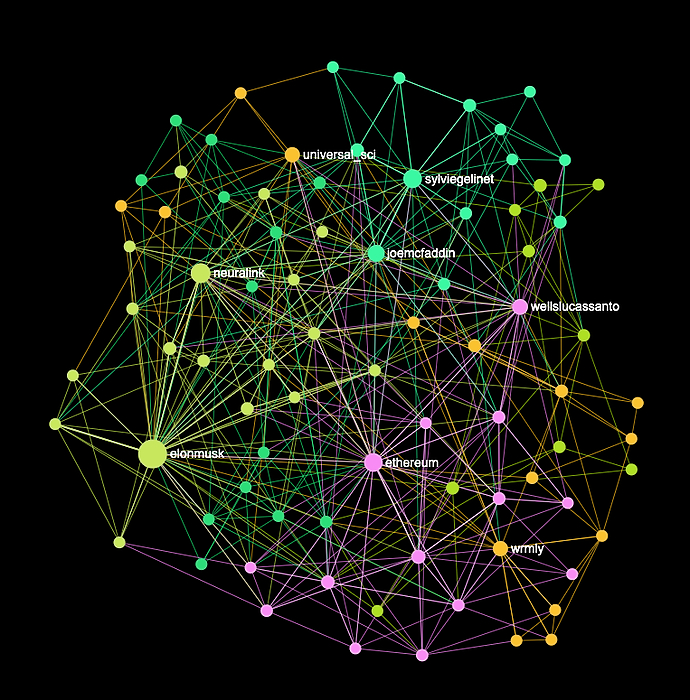
1. NFT'ers! LET'S GET READY TO RUMBLE!!! Polygon vs Solana
 Polygon and Solana are both promising projects with unique value propositions; comparing them does an injustice to both- but we will compare them anyway!
Polygon and Solana are both promising projects with unique value propositions; comparing them does an injustice to both- but we will compare them anyway!
2. Data Science Training and Data Science - Machine Learning With Python
 The requirement for its stockpiling also grew as the world entered the period of huge information. The principle focal point of endeavors was on structure framework and answers for store information. When frameworks like Hadoop tackled the issue of capacity, preparing of this information turned into a challenge. Data science began assuming a crucial job to take care of this issue. Information Science is the fate of Artificial Intelligence as It can increase the value of your business.
The requirement for its stockpiling also grew as the world entered the period of huge information. The principle focal point of endeavors was on structure framework and answers for store information. When frameworks like Hadoop tackled the issue of capacity, preparing of this information turned into a challenge. Data science began assuming a crucial job to take care of this issue. Information Science is the fate of Artificial Intelligence as It can increase the value of your business.
3. The 5G Conspiracy Theorists Making Money Out of Covid-19
 If you have been following social media during this pandemic, and it’s hard to avoid it, you may have noticed that conspiracy theories about the origins of the virus are multiplying like weeds.
If you have been following social media during this pandemic, and it’s hard to avoid it, you may have noticed that conspiracy theories about the origins of the virus are multiplying like weeds.
4. Hyperledger Fabric: create a Blockchain Network in under 10 minutes [no scripts]
 One of the biggest pains of getting started with Fabric, even though it's a powerful framework, is getting the infrastructure to work. This small tutorial will get you up and running in less than minutes. No script. No pain.
One of the biggest pains of getting started with Fabric, even though it's a powerful framework, is getting the infrastructure to work. This small tutorial will get you up and running in less than minutes. No script. No pain.
5. 10 Types of IT Services Your Business Can Provide

6. Difference In LTE And VoLTE Network.

7. The pyftpdlib Library and How to Transfer Files Over the Network Between Different Devices
 Transferring files over your network between your devices is a time-saving and effective way of moving data from one device to another without using hardware.
Transferring files over your network between your devices is a time-saving and effective way of moving data from one device to another without using hardware.
8. A Guide to Serial Terminal Servers: Secure Remote Access to a Serial Port
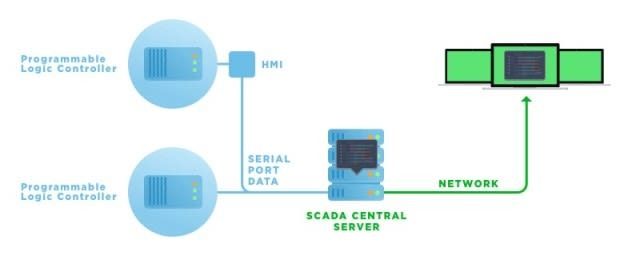 A Serial Terminal Server is a software or hardware solution designed to make a non-networked serial-based peripheral connect to the network through itself.
A Serial Terminal Server is a software or hardware solution designed to make a non-networked serial-based peripheral connect to the network through itself.
9. An Introduction to Layer 3 Switches
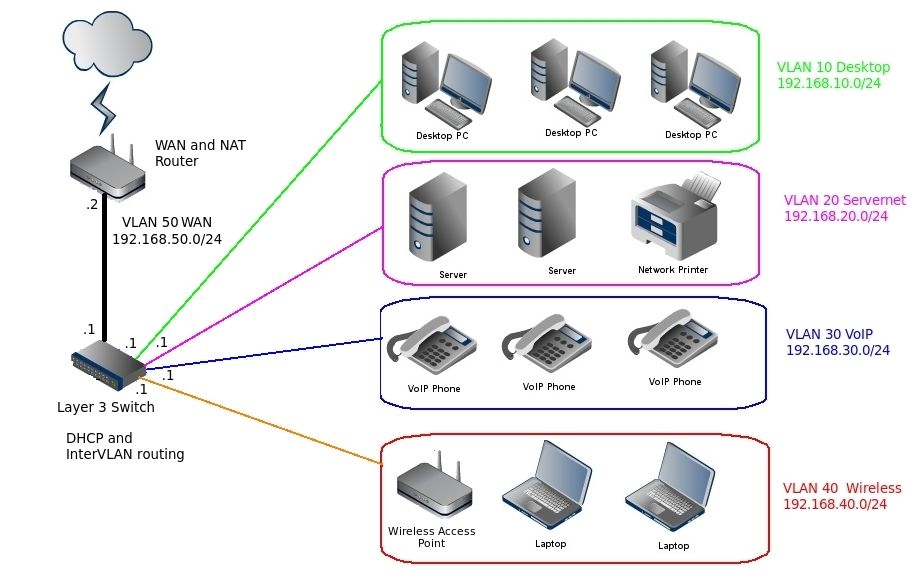 In today's complex business networks that comprise many virtual LAN's and subnets, a Layer 3 switch plays an important role in many systems. But do you need this on your network? Let's see.
In today's complex business networks that comprise many virtual LAN's and subnets, a Layer 3 switch plays an important role in many systems. But do you need this on your network? Let's see.
10. Nothing Can Stop Bitcoin, Not Even Governments
 In a nutshell, governments cannot take away your Bitcoin
In a nutshell, governments cannot take away your Bitcoin
11. Monitoring Bandwidth in Wi-Fi Networks: A Guide
12. Replicate PostgreSQL Databases Using async Python and RabbitMQ for High Availability
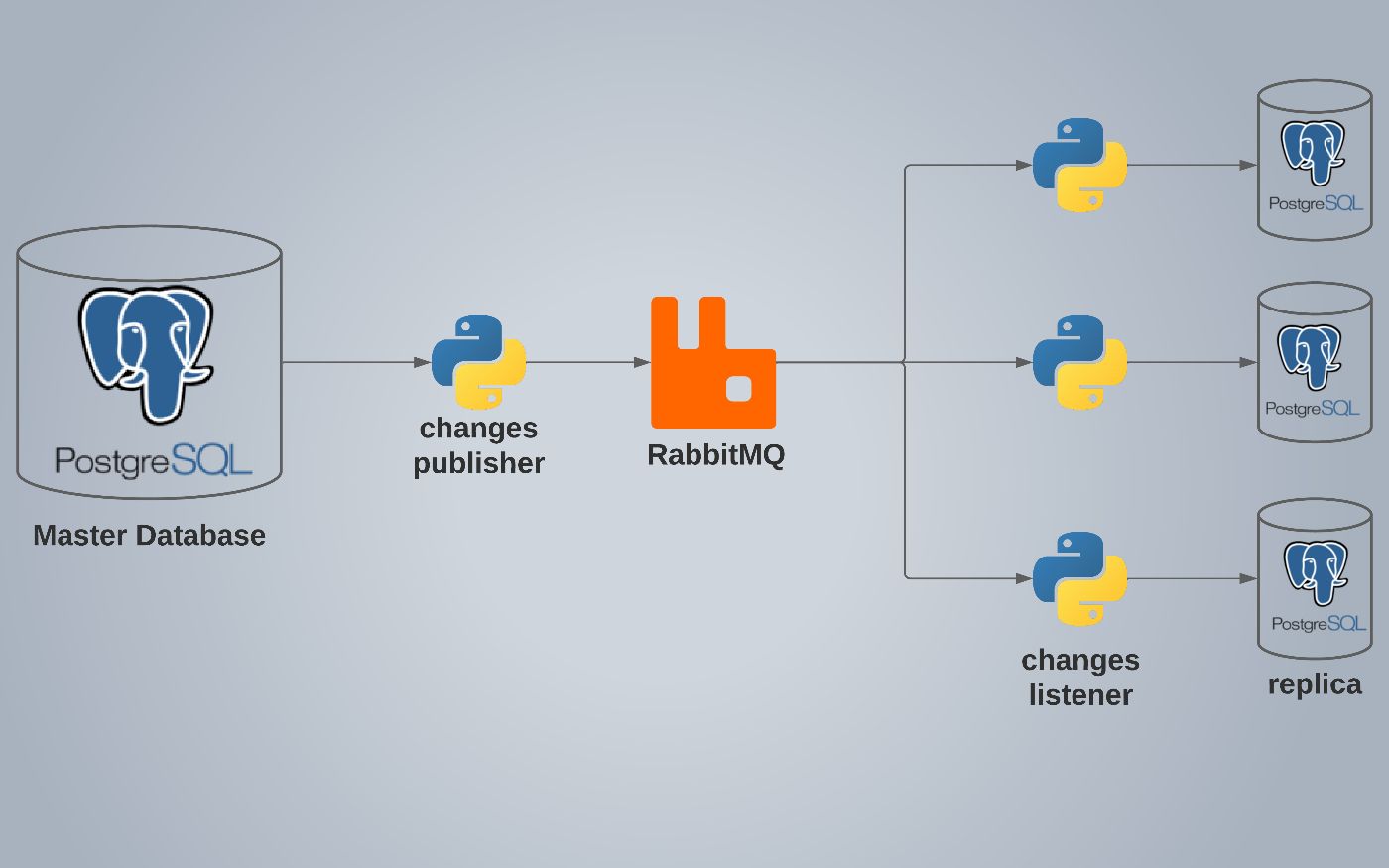 PostgreSQL replication using python and RabbitMQ for providing your database server with High Availability by easily making replicas of your master server.
PostgreSQL replication using python and RabbitMQ for providing your database server with High Availability by easily making replicas of your master server.
13. Can 5G Replace Broadband?
 With the breathless pace at which new digital innovations are emerging every day, many are now wondering when broadband will finally be rendered obsolete. Despite the possibility of alternatives like 5G taking over, however, many critics and proponents of broadband alike have yet to really determine once and for all whether it can replace broadband entirely.
With the breathless pace at which new digital innovations are emerging every day, many are now wondering when broadband will finally be rendered obsolete. Despite the possibility of alternatives like 5G taking over, however, many critics and proponents of broadband alike have yet to really determine once and for all whether it can replace broadband entirely.
14. How To Redirect USB Dongle: Hyper-V USB passthrough
 Majority of software programs require a hardware USB dongle in order to produce correct results. And what if you need to work with such a program in virtual environment where you cannot plug the dongle? There is no full-blown mechanism for connecting USB devices to virtual machine in Hyper-V, so when server is virtualized, all references with USB bus and USB devices connected to it are gone.
Majority of software programs require a hardware USB dongle in order to produce correct results. And what if you need to work with such a program in virtual environment where you cannot plug the dongle? There is no full-blown mechanism for connecting USB devices to virtual machine in Hyper-V, so when server is virtualized, all references with USB bus and USB devices connected to it are gone.
15. Your $1000 Smartphone Can Finally Pay For Itself

16. Why OpenTelemetry Should Matter to Network and Systems Admins
 OpenTelemetry is young, even by internet standards. Born out of the merger of OpenTracing and OpenCensus projects at the Cloud Native Computing Foundation CNCF
OpenTelemetry is young, even by internet standards. Born out of the merger of OpenTracing and OpenCensus projects at the Cloud Native Computing Foundation CNCF
17. Follow These Steps To Replay Browser’s Network Offline
18. Forget The Gig Economy, Join The Life Economy: Get Paid To Live

19. How Nutanix VM Works
 In the era of enterprise cloud, modern enterprise datacenter must support
virtualization with high availability and live VM migration. The traditional storage area networks (SAN) or network attached storage (NAS) doesn’t suit. Instead, they are ideal to manage a logical unit number (LUN). A LUN can be a single disk, an entire redundant array of independent disks (RAID), or disk partitions.
In the era of enterprise cloud, modern enterprise datacenter must support
virtualization with high availability and live VM migration. The traditional storage area networks (SAN) or network attached storage (NAS) doesn’t suit. Instead, they are ideal to manage a logical unit number (LUN). A LUN can be a single disk, an entire redundant array of independent disks (RAID), or disk partitions.
20. Linux Postfix-How to Add OpenDKIM to DNS
 Outsourcing is the process of a company contracting with a third party to do a certain task. This post will show how these two elements can work together.
Outsourcing is the process of a company contracting with a third party to do a certain task. This post will show how these two elements can work together.
21. Improve Network API Performance For Your Apps
 Network APIs are everywhere in the modern world. If the data is the lifeblood of modern tech, then APIs are essentially vessels that carry it around distributed
Network APIs are everywhere in the modern world. If the data is the lifeblood of modern tech, then APIs are essentially vessels that carry it around distributed
22. The Common Properties of All Great VPN Networks
 Virtual Private Networks (VPNs) are the pinnacle of the security and privacy industry. They allow for companies and individuals to get access to some restricted services and access other websites that they might not be able to access on their own.
Virtual Private Networks (VPNs) are the pinnacle of the security and privacy industry. They allow for companies and individuals to get access to some restricted services and access other websites that they might not be able to access on their own.
23. NAS Data Backup Is Essential For Remote Offices
 Network Attached Storage (NAS) is a smart, dedicated data storage system that connects to storage drives, allowing multiple users to collaborate and share data.
Network Attached Storage (NAS) is a smart, dedicated data storage system that connects to storage drives, allowing multiple users to collaborate and share data.
24. How To Use Keras To Train Neural Networks
 Keras is a deep learning framework for Python for building neural networks and training them on datasets. It can leverage GPUs and CPUs for training algorithms.
Keras is a deep learning framework for Python for building neural networks and training them on datasets. It can leverage GPUs and CPUs for training algorithms.
25. Why The CCIE is My Favorite Intro Level Certification
 The CCIE certification has two other key benefits beyond opening the door to a deeper appreciation of the knowledge continuum in its area of expertise.
The CCIE certification has two other key benefits beyond opening the door to a deeper appreciation of the knowledge continuum in its area of expertise.
26. Who Is Going to Benefit From 5G Network?
 With the creation of the Internet, the whole world was turned upside down. It became possible to contact one person to one side of the world from the other side of the world. We can find everything, play online and work conveniently.
With the creation of the Internet, the whole world was turned upside down. It became possible to contact one person to one side of the world from the other side of the world. We can find everything, play online and work conveniently.
27. How Will SpaceX Affect Satellite Tech Evolution and Network Adoption for Cruises?
 While it’s clear that SpaceX will force satellite providers to speed up tech development, how it will affect an industry such as cruise lines?
While it’s clear that SpaceX will force satellite providers to speed up tech development, how it will affect an industry such as cruise lines?
28. How to Maintain Good Network Infrastructure to Keep Data Flowing at Your Nonprofit
 It's imperative for your nonprofit to have a good network infrastructure. Here are a few tips to make sure it's the best it could be.
It's imperative for your nonprofit to have a good network infrastructure. Here are a few tips to make sure it's the best it could be.
29. Rethinking Programming: The Network in the Language
 With the emergence of microservices architecture, applications are developed by using a large number of smaller programs. These programs are built individually and deployed into a platform where they can scale independently. These programs communicate with each other over the network through simple Application Programming Interfaces (APIs). With the disaggregated and network distributed nature of these applications, developers have to deal with the Fallacies of Distributed Computing as part of their application logic.
With the emergence of microservices architecture, applications are developed by using a large number of smaller programs. These programs are built individually and deployed into a platform where they can scale independently. These programs communicate with each other over the network through simple Application Programming Interfaces (APIs). With the disaggregated and network distributed nature of these applications, developers have to deal with the Fallacies of Distributed Computing as part of their application logic.
30. Sending UDP Messages on Linux: What is the Condition to Packets Being Lost?
 In developing the distributed software system it might be reasonable to use exchange data over the UDP protocol to minimize exchange time.
In developing the distributed software system it might be reasonable to use exchange data over the UDP protocol to minimize exchange time.
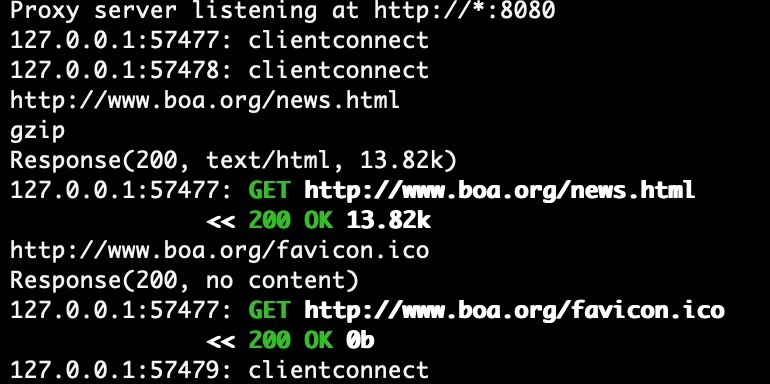
31. Overview of Android Networking Tools: Receiving, Sending, Inspecting, Mock Servers
 Overview of Android Networking Tools: Receiving, Sending, Inspecting, Mock Servers
Overview of Android Networking Tools: Receiving, Sending, Inspecting, Mock Servers
32. What Can Recurrent Neural Networks in NLP Do?
 Recurrent Neural Networks (RNN) have played a major role in sequence modeling in Natural Language Processing (NLP) . Let’s see what are the pros and cons of RNN
Recurrent Neural Networks (RNN) have played a major role in sequence modeling in Natural Language Processing (NLP) . Let’s see what are the pros and cons of RNN
33. IT Policy and Procedures Are Crucial To Your Business: Learn Why

34. Port Forwarding for Noobs
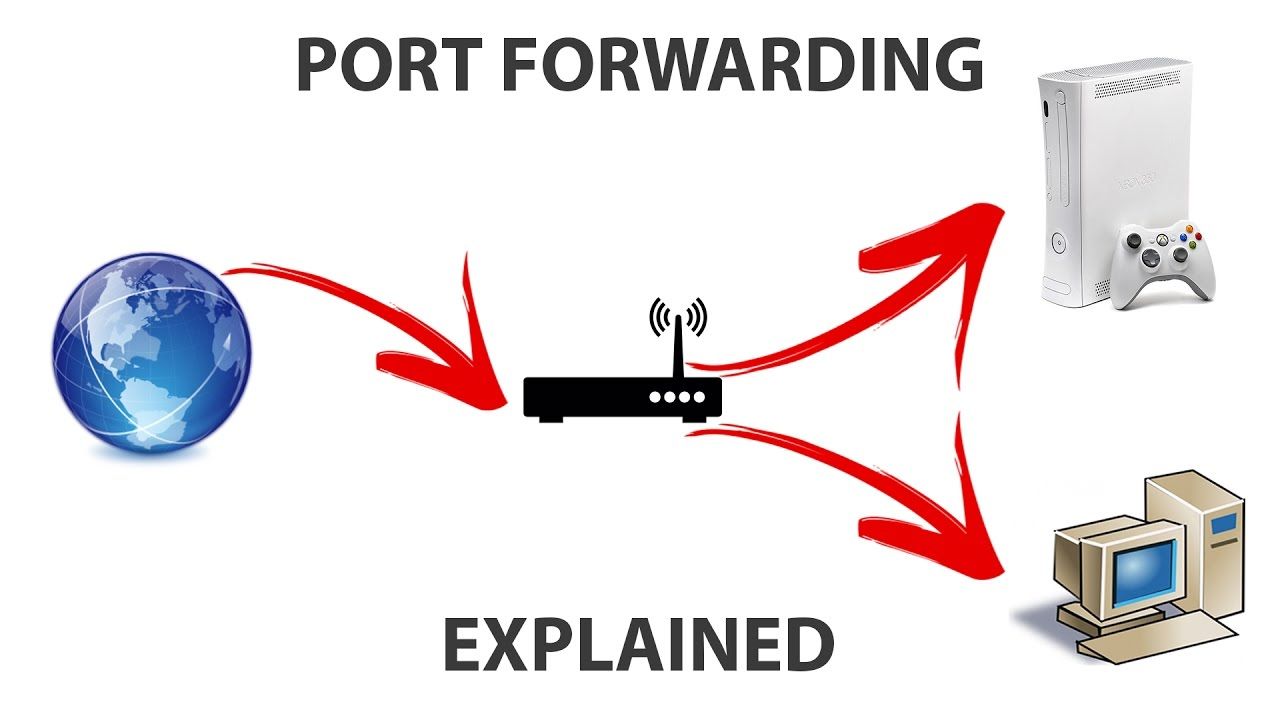 Port forwarding is used to enable a router to use a specific port to communicate with certain devices on a network. Learn more about how it is set up here.
Port forwarding is used to enable a router to use a specific port to communicate with certain devices on a network. Learn more about how it is set up here.
35. I Have My Own AWS VPC, and Now You Can Too!
 Let's see how a default VPC is configured in AWS, CIDR block, the associated subnets within it, routes, NACLs and Security Groups.
Let's see how a default VPC is configured in AWS, CIDR block, the associated subnets within it, routes, NACLs and Security Groups.
36. Major Reasons Why You Have Wi-Fi Dead Zones
 In the event that you have certain rooms or regions in your home where the Wi-Fi signal is moderate or nearly non-existent, you may have a Wi-Fi no man’s land. Does it take everlastingly to stack a page on the PC in your room? Is it practically difficult to watch Netflix in the cellar? No man’s lands and moderate zones can cause your gushing sticks, PCs, and savvy home gadgets to run ineffectively, conflictingly, or in some cases, not under any condition.
In the event that you have certain rooms or regions in your home where the Wi-Fi signal is moderate or nearly non-existent, you may have a Wi-Fi no man’s land. Does it take everlastingly to stack a page on the PC in your room? Is it practically difficult to watch Netflix in the cellar? No man’s lands and moderate zones can cause your gushing sticks, PCs, and savvy home gadgets to run ineffectively, conflictingly, or in some cases, not under any condition.
37. WTF is Network Slicing?

38. Network Information API: How to Access Network Connection Speed Info
 This is an experimental technology
Check the Browser compatibility table carefully before using this in production.
This is an experimental technology
Check the Browser compatibility table carefully before using this in production.
39. How to Boost Your Mind Viral Immunity
 TL;DR Diversity is the key
TL;DR Diversity is the key
40. How to Make a Malicious USB Device and Have Some Harmless Fun
 Make an inexpensive BadUSB from an old USB drive and learn about Windows shortcut files and how malicious actors are using .lnk files to spread malware.
Make an inexpensive BadUSB from an old USB drive and learn about Windows shortcut files and how malicious actors are using .lnk files to spread malware.
41. Man In The Middle Attack Using Bettercap Framework
 Man-in-the-middle attack (MITM) is an attack where the attacker secretly relays and possibly alters the communications between two devices who believe that they are directly communicating with each other. In order to perform man in the middle attack, we need to be in the same network as our victim because we have to fool these two devices. Now lets initiate the attack by running our tools which is bettercap. To run bettercap we can simply open up terminal and type bettercap -iface [your network interface which connected to the network]. To know which network interface is used we can simply type ifconfig and here is what it shows us.
Man-in-the-middle attack (MITM) is an attack where the attacker secretly relays and possibly alters the communications between two devices who believe that they are directly communicating with each other. In order to perform man in the middle attack, we need to be in the same network as our victim because we have to fool these two devices. Now lets initiate the attack by running our tools which is bettercap. To run bettercap we can simply open up terminal and type bettercap -iface [your network interface which connected to the network]. To know which network interface is used we can simply type ifconfig and here is what it shows us.
42. A Guide to Network Gadgets that Contain Ping, NTP, TFTP, and Iperf
43. Creating Our Own Custom Messaging Solution for IoT Devices
 The Internet of Things relies on the interoperation of network nodes. Integra created a custom technology that improved client-server interaction.
The Internet of Things relies on the interoperation of network nodes. Integra created a custom technology that improved client-server interaction.
44. A Step By Step Guide To Becoming A Network Engineer
 Businesses are depending more than ever on networked devices to execute routine activities. As a result, they frequently require network engineers' assistance in the design, construction, setup, and maintenance of their computer networks. Learning how to start a network engineering profession might allow you to determine if this is the best path for you. In this post, we will cover what network engineering comprises and how to become a network engineer.
Businesses are depending more than ever on networked devices to execute routine activities. As a result, they frequently require network engineers' assistance in the design, construction, setup, and maintenance of their computer networks. Learning how to start a network engineering profession might allow you to determine if this is the best path for you. In this post, we will cover what network engineering comprises and how to become a network engineer.
45. Differences Between RFID and NFC Systems, their Applications, and Alternatives
 RFID and NFC are similar communication methods that devices can use to interact with each other. However, there are differences in the systems and usage.
RFID and NFC are similar communication methods that devices can use to interact with each other. However, there are differences in the systems and usage.
46. How to Map Your Home Networks Using NMAP
 Here's to learning basics of networking and an awesome tool called NMAP
Here's to learning basics of networking and an awesome tool called NMAP
Thank you for checking out the 46 most read stories about Network on HackerNoon.
Visit the /Learn Repo to find the most read stories about any technology.

